
Modernize and Consolidate Identity Security
Modern attackers don't break in; they log in. Download our practical framework for modernizing identity security before it becomes a material event.
↓ Download the Free GuideThe Identity Security Gap Your Existing Tools Can't Close
Over the last decade, enterprises have invested heavily in IAM, IGA, PAM, MFA, and SIEM platforms. These tools are foundational to providing access, enforcing policy, authenticating users, and logging events.
But modern breaches no longer stop at authentication. They exploit identity after login.
Stolen OAuth Tokens
Valid tokens bypass MFA entirely — no password needed.
Session Hijacking
Attackers inherit authenticated sessions undetected.
Service Account Misuse
Unmonitored NHIs used as silent lateral movement vehicles.
Lateral Movement
Spread via valid credentials that appear legitimate in logs.
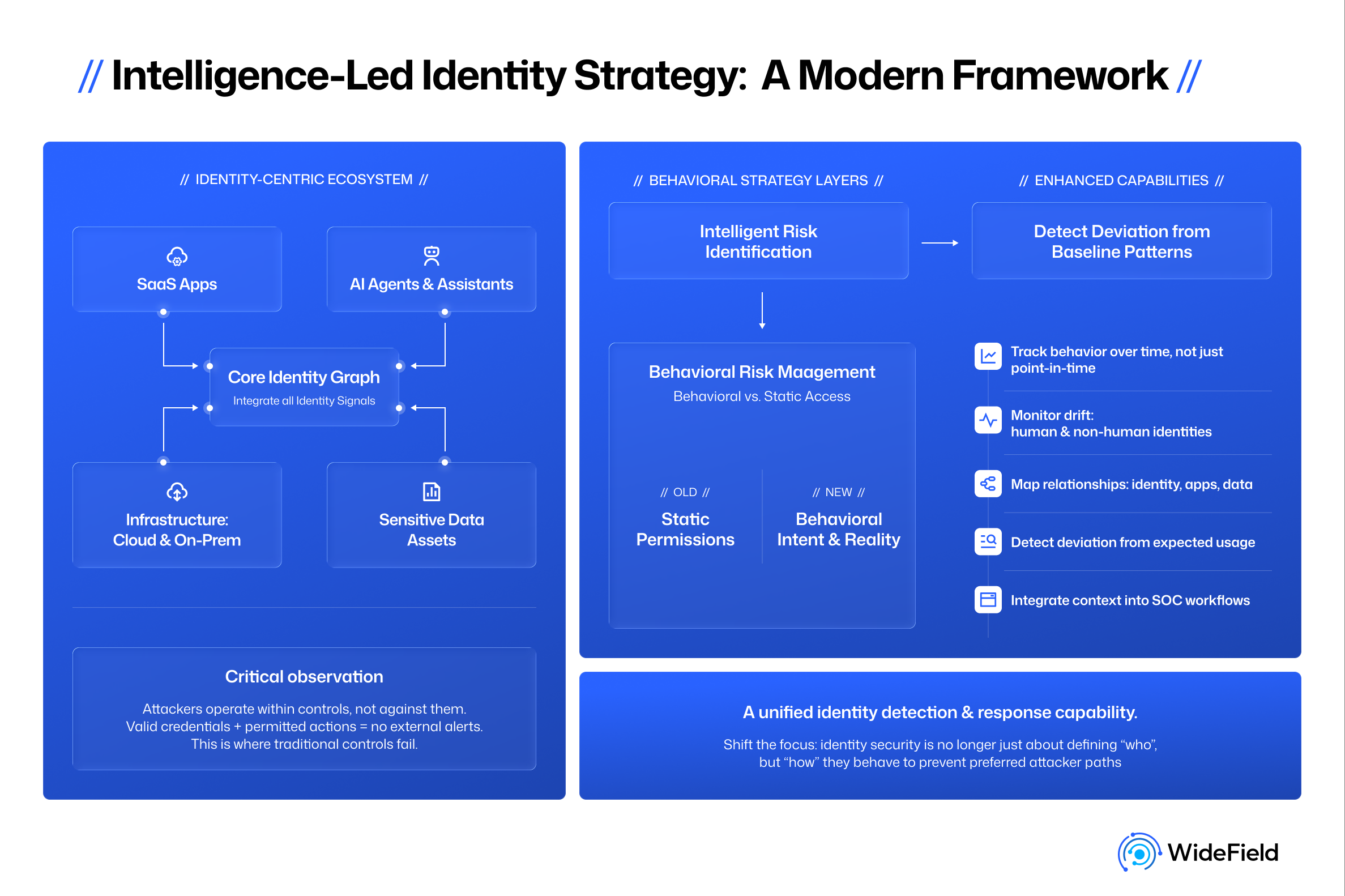
Traditional identity and logging systems lose contextual visibility the moment access is granted. The attack surface has shifted from authentication to identity-in-use; yet, most organizations have no coverage there.
Three Identity Risk Areas Most Organizations Underestimate
The guide walks through a structured risk assessment across the three threat categories CISOs consistently underestimate — with practical diagnostic questions for each.
Identity Hygiene Gaps
Dormant accounts, orphaned service accounts, privilege creep, and partially off-boarded users create silent exposure across SaaS and cloud environments, well beyond what your IAM system reports.
AI Agent and Non-Human Identity Risk
NHIs now outnumber human identities in most enterprises by 144x. They rarely use MFA, often hold elevated privileges, and lack behavioral baselines — making them ideal targets for quiet lateral movement.
Session & Token-Based Threats
Modern attackers avoid passwords entirely. They steal active session tokens, exploit OAuth device code flows, and abuse third-party app permissions — all of which look legitimate in traditional logs.
What a Modern ITDR Platform Must Deliver
Not all identity security tools are built for the post-authentication threat landscape. The guide defines four pillars every CISO should demand from a modern ITDR platform:
Comprehensive Identity Visibility
Unified discovery across SaaS, cloud, and hybrid environments for AI agents, non-human identities, and your human identities alike, including credential inventory and OAuth grant risk scoring.
Behavioural Detection Across Identity Types
Static rules are insufficient. ITDR must model identity at rest, in motion, and in use, enabling the detection of service account misuse, parallel sessions, and abnormal privilege escalation.
Response & Containment
Detection without response creates backlogs. Response actions, such as session revocation or identity disablement, must execute within minutes, not days.
Signal Quality & Operational Efficiency
The goal is fewer, better alerts. High-fidelity, explainable detections reduce SOC burden and analyst fatigue — translating directly into retention and cost savings.
Why Identity Security Is Now a Board-Level Conversation
ITDR investment aligns directly with three priorities that executive leaders and boards are actively tracking:
Zero Trust Maturity: Without session-layer monitoring, Zero Trust is incomplete. ITDR is the operational layer that makes continuous verification real — not theoretical.
Risk Reduction & Dwell Time: Even a modest reduction in breach probability produces significant economic return. ITDR compresses the window between compromise and containment.
Compliance & Audit Readiness: Boards increasingly demand evidence of identity oversight. ITDR provides audit trails, remediation documentation, and continuous access verification reporting.
A Defensible Business Case in Three Calculations
The guide provides a concrete investment justification framework. Here's a preview of the three dimensions:
Risk Reduction Value
Quantify the financial exposure of an identity-led breach against the probability reduction ITDR delivers.
Operational Efficiency
Calculate SOC hours recovered through reduced alert volume and faster investigation workflows.
📥 The full framework, including the 10-point ITDR Evaluation Checklist, is available in the free download below.
Get the Full Guide: Making the Case for ITDR
Everything you need to assess your identity risk exposure, evaluate vendors, and build a board-ready business case.